In today’s KB 4583468 and CVE 2021 1636, Microsoft is fixing vulnerabilities in Extended Events that “may cause code to run against the SQL Server process if a certain extended event is enabled.” I, for one, throw 100% of the blame on Team Profiler, who surely hacked SQL Server in an effort to discredit Team XE.
Tons of patching to do here:
- SQL Server 2019 CU8 GDR
- SQL Server 2017 CU22 GDR
- SQL Server 2016 SP2 CU15 GDR
- SQL Server 2014 SP3 CU4 GDR
And there are GDRs for other patch levels too, like if you’re on 2016 but not on SP2 yet.
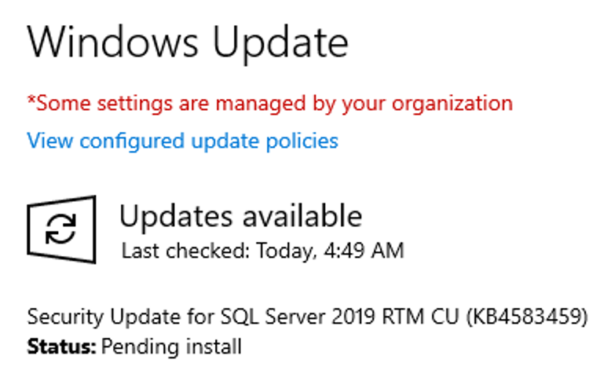
Update: it’s distributed via Windows Update, too.
16 Comments. Leave new
I couldnt find it listed as to what the EE was. Did they reveal it?
No, and given the security risk – attackers *own* the server – I wouldn’t expect them to reveal it publicly anytime soon. It takes forever to get folks patched.
Any idea of what event exactly? I read the KB and CVE but it seems that MSFT is not disclosing that information. It would be nice to know, though, to see what servers need immediate action and which ones I could take more time to test the patch.
And yeah, Team Profiler must be behind this heinous discredit effort XD
Aaron – given the security risk – attackers *own* the server – I wouldn’t expect them to reveal it publicly anytime soon. It takes forever to get folks patched.
Oh, nvm. I just saw Brent’s response to Dan White.
Hello Brent,
Why you don’t speak about KB4583465 – Description of the security update for SQL Server 2012 SP4 GDR: January 12, 2021 ?
It’s also for KB4583468, no?
Kind regards,
Jean-Luc
Jean-Luc – make sure to read through the whole entire post. I know it’s a long one – may need to make some coffee or shut off the distractions – but I have faith in you. I know if you really buckle down and work at it, you can make your way all the way to that last sentence there. 😉
Wait a sec… XE is a feature of SQL 2008 too, but that version is not listed as affected. Could it be because it’s not affected or because it’s out of support?
I suppose because it’s out of support
So, when I follow the links to the Microsoft KB’s, I see a note at the bottom:
“This update is made available through the Microsoft Update Catalog for all servers that are running SQL Server, even if Reporting Services is not installed. Installing this security update is optional for computers that do not host Microsoft SQL Server Reporting Services.”
We have just a handful of SSRS instances. So I guess I really just need to focus on them, and not our entire MSSQL footprint?
I don’t have insider information, but I wonder whether MS wrongly copied that section from the article for the *previous* Security Update – CVE-2020-0618 – which *was* for SSRS. On the face of it the details disclosed for the new one don’t sound “SSRS-only”, do they…?
If anyone can clarify, please do share here!
Does this vulnerability effect SQL2008 R2. I know its not listed because its out of support but would it be covered by any Extended Support Agreements?
Your best bet there would be to contact Microsoft if you have an Extended Support Agreement.
Has anyone figured out if this applies to Express Editions?
I. E., do we need to get workstation support / patch management involved to address workstation installs for “software X”?
(and hey… what about WID?)
Does Express Edition have Extended Events?
Unsure if it applies from a technical standpoint but I do get a ping from my vulnerability detection on CVE-2021-1636 for systems with SQLExpress 2019. Would be nice if it could be clarified if this is a detection issue identifying SQLExpress as full SQL or if the vulnerability actually applies to SQLExpress. Any information on this would be very helpful.